Malware and phishing attacks aren’t new. They aren’t rare either. We have clever and effective antimalware programs on almost every machine in corporate environments. So how can it possibly be true that so many IT departments, even in large profitable organizations, are getting caught flat-footed by this menace?
The problem — users. The trouble is that your users don’t think like an antimalware program. It’s time to change their way of thinking.
According to a study by Cyber Security Ventures, extortion via ransomware is expected to cost companies $5 billion in 2017. Antivirus and antimalware programs should take care of much of the malware, but the biggest loophole hackers use is user naivety. It’s users that cause the biggest risk to an enterprise network, and an IT administrator is nearly defenseless against human error.
The primary security a IT manager can use against phishing is educating users — and getting them to
act on that education. This “antivirus for the brain” gives users the logic tools to identify phishing and other malware attacks. They can report it and/or simply delete the email. Email is the most common form of attack, because an attacker can send thousands of messages at a time. In marketing terms, email has the best ROI for the attacker. It’s cheap and effective.
How Malware Works and How Antimalware Protects Against It
Most IT professionals know how malware works, but users often do not. To help your users do the right thing, it helps to have them at least know the basics. Below, in simple laymen’s terms, is a short description of the main types of malware. You might want to copy these descriptions and send to all your users (or use in your program to train them).
- Virus: malware that self-replicates and infects files, usually attaching itself to Windows programs. At one time, the term “virus” was often used as a generic term for anything that could harm a computer or network. Now the term malware is more common when describing multiple types.
- Trojan: a seemingly harmless program delivered by hiding within something else. It often comes in an innocuous-looking email attachment or some freeware. The name is a fitting throwback to the legend of the Trojan Horse, wherein the Greeks hid about thirty warriors inside a huge wooden horse and left it on a beach outside of the massive walls of the fortress of Troy (a city that is now part of Turkey), just before appearing to sail away.
 The Trojans, believing the ornamented horse to be abandoned by a fleeing army, pulled it through the gates and into their fortress city as a spoil of their victory. Late that night, the Greek warriors crept out of a door concealed in the wooden horse, overwhelmed the small force of Trojan guards and opened the gates to let in the rest of the Greek battalion that had sailed back under the cover of night, allowing the Greeks to destroy the unprepared Trojan army (and their city) from inside. As with the legend from whence it gets its name, Trojan malware appears harmless. But once it’s let inside your network, it can do almost anything nefarious, including, but not limited to disrupting computer processes, stealing sensitive information, like PII (Personally Identifiable Information), deleting files or programs, and blocking access to data.
The Trojans, believing the ornamented horse to be abandoned by a fleeing army, pulled it through the gates and into their fortress city as a spoil of their victory. Late that night, the Greek warriors crept out of a door concealed in the wooden horse, overwhelmed the small force of Trojan guards and opened the gates to let in the rest of the Greek battalion that had sailed back under the cover of night, allowing the Greeks to destroy the unprepared Trojan army (and their city) from inside. As with the legend from whence it gets its name, Trojan malware appears harmless. But once it’s let inside your network, it can do almost anything nefarious, including, but not limited to disrupting computer processes, stealing sensitive information, like PII (Personally Identifiable Information), deleting files or programs, and blocking access to data.
- Worm: an application that replicates malicious programs that take up bandwidth and slow systems. They are little programs that run in the background, using up the computer’s resources and potentially taking other harmful actions.
- Spyware: programs that steal sensitive data and log user browsing history. You may never know that you’ve had spyware. The programs can get into the computer, email the desired information to the hackers, then hide or delete themselves.
- Logic bomb: malware that lies dormant until a certain criteria is met, either a date is reached, or some other event, at which time it deploys its payload (“explodes”). For example, a company employee can use a logic bomb to install a set of instructions that will automatically be implemented when his name disappears off the payroll.
- Ransomware: malicious programs that encrypt important files and hold them ransom until the user pays a fee.
Ransomware is the current popular way for attackers to make money and steal data, and it’s quickly becoming the prevalent malicious attachment. Sometimes the creators of ransomware use other forms of malware, such as Trojans and worms, to deliver and disguise the ransomware programs and ensure that the victim is infected.

Any macro should be a red flag for users. Macros are one of the most common ways to infect a machine, because it’s common for users to run macros in files attached to email messages. The user thinks nothing of the file attached to the email, opens it, and allows the macro to run. The macro connects to a remote server and downloads ransomware silently in the background.
The malware places its own executable in the Windows registry key, so that the next time the user reboots their machine the ransomware is able to run. Current versions of Office disable macros by default, displaying a popup window asking if the user wants to run the macro. If the user is the trusting type, laissez faire (which interestingly translates to “let do”) and they just routinely click “Yes” to everything, they’re endangering the entire network and the company itself.
The first defense an administrator runs to is email filters and antimalware protection. The purpose of an email filter is to stop the attack at the email server, so the user never even has the chance to make the decision to download malware. Even here though, the user can derail the best plans to protect the network. If a user can simply look through the filtered emails and allow one that shouldn’t be allowed, an intrusion can happen.
Antimalware is a secondary defense that works in case malware is run on the machine. Antimalware works with a signature file, which is a database of binary patterns. These signatures are binary patterns found in malware that provides a way for antimalware software to detect it. Before malware can load into computer memory, antimalware intercepts the program, scans the binaries and compares them to the large database of signatures. This is how antimalware programs are able to identify and stop a program from loading into memory and infecting the machine.
All administrators know that for antimalware to remain effective, these signature files must be regularly updated. New malware is released every day, so antimalware companies create updates for the signature database every week. If a user runs malware on their machine with old signature files, then an antimalware program is unable to detect it. It’s what makes zero-day viruses so efficient and successful. The same datum applies to users. When new information comes out about new threats, let them know. Keep them up to date, just like you keep programs up to date.
According to the independent IT security institute,
AV Tests, there are 390,000 new malware programs released to the public every day. Antimalware is useless against
some of these new programs until antimalware developers have a chance to discover their signatures and distribute new signature database files. This can take anywhere from a few days to a month, so your network is vulnerable even with the best defense in place.
Installing Antivirus in Your Users’ Brains
Much to the lament of IT pros and business owners everywhere, there’s no way to install antimalware applications into the human brain (well, no
safe way) — yet. Until that day comes, it’s all about education and training. Your end-users need to know what to look for every time they receive an email. Even if the email is from a fellow employee, they should be suspicious. Users don’t know how to read email headers, so they won’t be able to identify a spoofed sender from the real thing. IT professionals know that a common malware trick is to scan contacts in an email address list and send malicious attachments from the victim to their contact list. But users don’t know this, unless they’ve been specifically taught.
Let’s look at some examples to show users what they can look for and understand what attackers are doing when they send messages. This is a phishing email:
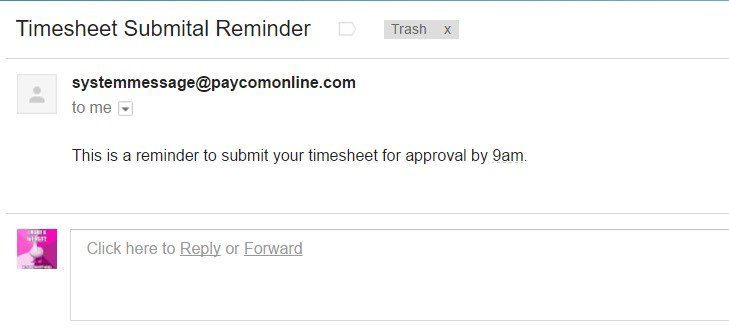
Recently, DocuSign was hacked. They notified users that email addresses were stolen. When this happens, often phishing emails are sent to the list of breached accounts.
The above email was sent to the email addresses obtained in the DocuSign attack. It looks like a harmless message. There is no “call to action” to lure the user into downloading a program or clicking a link. Looking at paycomonlein.com, it looks like it’s a legitimate payroll services site, so it’s a good assumption that the site has been hacked. Most users receiving this email won’t have a paycomonline.com account and won’t use it to submit timesheets.
Though this email looks benign, there is a reason for an attacker to use it. The main objective is to see whether the email is active and can receive messages. This information is very useful for the attacker.
Some users would even reply to this email. Replying to the email tells the hacker that the user doesn’t suspect it’s malicious, and allows the attacker to add the user to his “could fall for a phishing attack” list.
The attacker sometimes puts an “unsubscribe” link in the email to trick a user into accessing his private server. This lets the attacker know that the email went directly to the inbox instead of the recipient’s spam box, and it’s a positive signal that the user didn’t recognize that it’s bogus.
This is what your users (when thinking like antimalware) should ask themselves if they receive an email like the above image:
- Do I use this payroll program?
- Why does it not address me by name?
- Would a professional payroll service send me a one-line automated email message without addressing me by name or providing a well-thought-out message?
- Why is there no contact information?
It’s more common for phishing attackers to trick users into entering credentials at a malicious site. Let’s take a look at another phishing email.
As an IT person, this probably looks incredibly obvious. But
Microsoft research has shown that scammers intentionally use obviously bogus messages, for a very clever reason. It allows them to locate the very best targets, those most likely to fall for their scam. You might think no one could possibly fall for this scam, but this sender was probably successful with some recipients.
This message was flagged by the spam filter, of course. But even without the spam notification, there are several red flags that are obvious. Obvious to
you, but not to many of your end users. Your challenge is to train your users to think critically, to look for illogical factors, by covering data such as the following.
In this example, the
first sign to point out to your users is the language used in the signature. Any professional business matches the signature text with the language of the recipient. If you look at the citromail.hu domain, you’ll see that this is a free email distributor that has no quality checks and balances. Any free email domains including Hotmail, Outlook, Gmail, and Yahoo should automatically send red flags. It doesn’t mean all emails sent from these addresses are malicious, but your users should always take special precautions when receiving emails from these domains.
You can’t see it from this message, but hovering over the link gives you a shortlink. Users should immediately see this as a red flag. Behind the shortlink is a site that distributes malware. The same shortlink is used in the signature. Attackers use shortlinks to avoid malicious link detection from server filters.
This is what your users should ask themselves if they receive an email like the above image:
- Why is the sender using a free email domain for a professional email?
- Why is the signature in a different language than the message?
- Where does the shortlink go? It’s safe to hover over it and see the text of the link. If it goes to an unfamiliar site, or anything that doesn’t make sense, the user should never click on it.
PayPal
PayPal is one of the most commonly used official sites spoofed by attackers. Here is an example of an email attempting to gain access to financials.
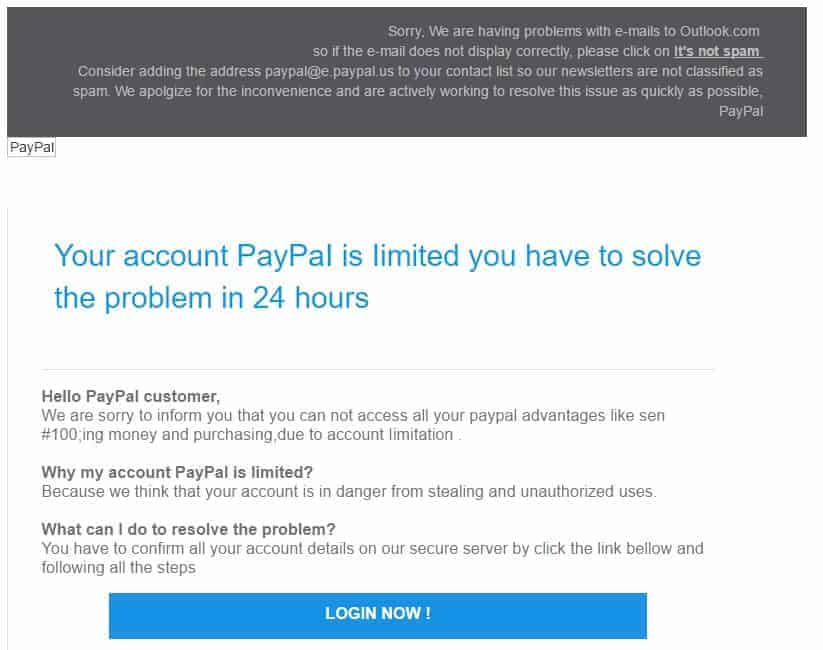
This email was also sent from a free email domain, but there are several new issues with this attempt. First, the attacker tries to get the user to click “Not Spam” in their email client to allow them to stop the filters from sending their messages to spam.
The English is extremely poor, and users should realize that the real PayPal would never send such a poorly worded email. Also, there are some technical errors in the content.
Hovering over the “Login Now” button shows you a different domain than the official PayPal domain. Again, users must be taught the difference between hovering (safe) and clicking (not safe).
This is what your users should ask themselves if they receive an email like the above image:
- Why would PayPal send messages from a Gmail account?
- Why is the grammar and spelling terrible?
- Why does the Login button take me to a domain that isn’t PayPal?
- Why is there no signature that leaves a contact number to call PayPal?
These three images are just a few examples, but the same red flags are there. Your users need to put on their “antivirus hat” and recognize malicious emails for what they are —malicious.
We didn’t include the lottery or Nigerian prince scams. These scams are decades old, but users still fall victim to them. It shows that the biggest problem facing administrators, when it comes to phishing, emails and malware, is user education.

Plenty of consultants try to educate users, but the best way to approach it is to have samples of phishing emails and show users what to look for. Consultants or IT people rarely show users example emails, and this is one reason why security education fails. Just look in your spam folder, and you can find dozens of examples.
If you’re lacking examples, type “online pharmacy” in Google and use a throwaway address to sign up to every site you find. Within days, you will get phishing emails that you can use to educate users.
If you think user education isn’t important, this should change your mind. The security software company Barkly reported on a study which tested how people really behaved when confronted with clever phishing attempts. In the test, 45% of users clicked through on a phishing email but only 20% admitted to it. It’s common for users to keep the fact that they fell for a scam a secret, but you can empower them to understand the signs so that they never engage the attacker.
The Barkly study also reports that there were more phishing attacks in Q1 2016 than in any three-month period since they began tracking it in 2004. IT can only do so much with antimalware and email filtering. You must educate your users to stop the attacks before they become a nightmare on your system. Here are some basic tips to give users more confidence and defend against phishing:
- Show them real-life examples.
- From these examples, show them malicious sites that look to obtain private credentials or financial data.
- Help them understand what happens after they send credentials to a hacker’s server.
- Warn them that social media is one of the major surveying and reconnaissance tools for an attacker.
- Teach them to always be suspicious of any email that has an attachment even if it’s from an internal contact.
- Embolden them, so they will not be afraid to ask questions if you find something in an email suspicious.
- Make sure they know how important is to always report phishing attacks to IT.
Do all the above, and do it well, and your users will be a help, not a hindrance, in the battle to keep your data and your network safe from the bad guys.
 Malware and phishing attacks aren’t new. They aren’t rare either. We have clever and effective antimalware programs on almost every machine in corporate environments. So how can it possibly be true that so many IT departments, even in large profitable organizations, are getting caught flat-footed by this menace?
The problem — users. The trouble is that your users don’t think like an antimalware program. It’s time to change their way of thinking.
According to a study by Cyber Security Ventures, extortion via ransomware is expected to cost companies $5 billion in 2017. Antivirus and antimalware programs should take care of much of the malware, but the biggest loophole hackers use is user naivety. It’s users that cause the biggest risk to an enterprise network, and an IT administrator is nearly defenseless against human error.
The primary security a IT manager can use against phishing is educating users — and getting them to act on that education. This “antivirus for the brain” gives users the logic tools to identify phishing and other malware attacks. They can report it and/or simply delete the email. Email is the most common form of attack, because an attacker can send thousands of messages at a time. In marketing terms, email has the best ROI for the attacker. It’s cheap and effective.
Malware and phishing attacks aren’t new. They aren’t rare either. We have clever and effective antimalware programs on almost every machine in corporate environments. So how can it possibly be true that so many IT departments, even in large profitable organizations, are getting caught flat-footed by this menace?
The problem — users. The trouble is that your users don’t think like an antimalware program. It’s time to change their way of thinking.
According to a study by Cyber Security Ventures, extortion via ransomware is expected to cost companies $5 billion in 2017. Antivirus and antimalware programs should take care of much of the malware, but the biggest loophole hackers use is user naivety. It’s users that cause the biggest risk to an enterprise network, and an IT administrator is nearly defenseless against human error.
The primary security a IT manager can use against phishing is educating users — and getting them to act on that education. This “antivirus for the brain” gives users the logic tools to identify phishing and other malware attacks. They can report it and/or simply delete the email. Email is the most common form of attack, because an attacker can send thousands of messages at a time. In marketing terms, email has the best ROI for the attacker. It’s cheap and effective.
 The Trojans, believing the ornamented horse to be abandoned by a fleeing army, pulled it through the gates and into their fortress city as a spoil of their victory. Late that night, the Greek warriors crept out of a door concealed in the wooden horse, overwhelmed the small force of Trojan guards and opened the gates to let in the rest of the Greek battalion that had sailed back under the cover of night, allowing the Greeks to destroy the unprepared Trojan army (and their city) from inside. As with the legend from whence it gets its name, Trojan malware appears harmless. But once it’s let inside your network, it can do almost anything nefarious, including, but not limited to disrupting computer processes, stealing sensitive information, like PII (Personally Identifiable Information), deleting files or programs, and blocking access to data.
The Trojans, believing the ornamented horse to be abandoned by a fleeing army, pulled it through the gates and into their fortress city as a spoil of their victory. Late that night, the Greek warriors crept out of a door concealed in the wooden horse, overwhelmed the small force of Trojan guards and opened the gates to let in the rest of the Greek battalion that had sailed back under the cover of night, allowing the Greeks to destroy the unprepared Trojan army (and their city) from inside. As with the legend from whence it gets its name, Trojan malware appears harmless. But once it’s let inside your network, it can do almost anything nefarious, including, but not limited to disrupting computer processes, stealing sensitive information, like PII (Personally Identifiable Information), deleting files or programs, and blocking access to data. Any macro should be a red flag for users. Macros are one of the most common ways to infect a machine, because it’s common for users to run macros in files attached to email messages. The user thinks nothing of the file attached to the email, opens it, and allows the macro to run. The macro connects to a remote server and downloads ransomware silently in the background.
The malware places its own executable in the Windows registry key, so that the next time the user reboots their machine the ransomware is able to run. Current versions of Office disable macros by default, displaying a popup window asking if the user wants to run the macro. If the user is the trusting type, laissez faire (which interestingly translates to “let do”) and they just routinely click “Yes” to everything, they’re endangering the entire network and the company itself.
The first defense an administrator runs to is email filters and antimalware protection. The purpose of an email filter is to stop the attack at the email server, so the user never even has the chance to make the decision to download malware. Even here though, the user can derail the best plans to protect the network. If a user can simply look through the filtered emails and allow one that shouldn’t be allowed, an intrusion can happen.
Antimalware is a secondary defense that works in case malware is run on the machine. Antimalware works with a signature file, which is a database of binary patterns. These signatures are binary patterns found in malware that provides a way for antimalware software to detect it. Before malware can load into computer memory, antimalware intercepts the program, scans the binaries and compares them to the large database of signatures. This is how antimalware programs are able to identify and stop a program from loading into memory and infecting the machine.
All administrators know that for antimalware to remain effective, these signature files must be regularly updated. New malware is released every day, so antimalware companies create updates for the signature database every week. If a user runs malware on their machine with old signature files, then an antimalware program is unable to detect it. It’s what makes zero-day viruses so efficient and successful. The same datum applies to users. When new information comes out about new threats, let them know. Keep them up to date, just like you keep programs up to date.
According to the independent IT security institute, AV Tests, there are 390,000 new malware programs released to the public every day. Antimalware is useless against some of these new programs until antimalware developers have a chance to discover their signatures and distribute new signature database files. This can take anywhere from a few days to a month, so your network is vulnerable even with the best defense in place.
Any macro should be a red flag for users. Macros are one of the most common ways to infect a machine, because it’s common for users to run macros in files attached to email messages. The user thinks nothing of the file attached to the email, opens it, and allows the macro to run. The macro connects to a remote server and downloads ransomware silently in the background.
The malware places its own executable in the Windows registry key, so that the next time the user reboots their machine the ransomware is able to run. Current versions of Office disable macros by default, displaying a popup window asking if the user wants to run the macro. If the user is the trusting type, laissez faire (which interestingly translates to “let do”) and they just routinely click “Yes” to everything, they’re endangering the entire network and the company itself.
The first defense an administrator runs to is email filters and antimalware protection. The purpose of an email filter is to stop the attack at the email server, so the user never even has the chance to make the decision to download malware. Even here though, the user can derail the best plans to protect the network. If a user can simply look through the filtered emails and allow one that shouldn’t be allowed, an intrusion can happen.
Antimalware is a secondary defense that works in case malware is run on the machine. Antimalware works with a signature file, which is a database of binary patterns. These signatures are binary patterns found in malware that provides a way for antimalware software to detect it. Before malware can load into computer memory, antimalware intercepts the program, scans the binaries and compares them to the large database of signatures. This is how antimalware programs are able to identify and stop a program from loading into memory and infecting the machine.
All administrators know that for antimalware to remain effective, these signature files must be regularly updated. New malware is released every day, so antimalware companies create updates for the signature database every week. If a user runs malware on their machine with old signature files, then an antimalware program is unable to detect it. It’s what makes zero-day viruses so efficient and successful. The same datum applies to users. When new information comes out about new threats, let them know. Keep them up to date, just like you keep programs up to date.
According to the independent IT security institute, AV Tests, there are 390,000 new malware programs released to the public every day. Antimalware is useless against some of these new programs until antimalware developers have a chance to discover their signatures and distribute new signature database files. This can take anywhere from a few days to a month, so your network is vulnerable even with the best defense in place.
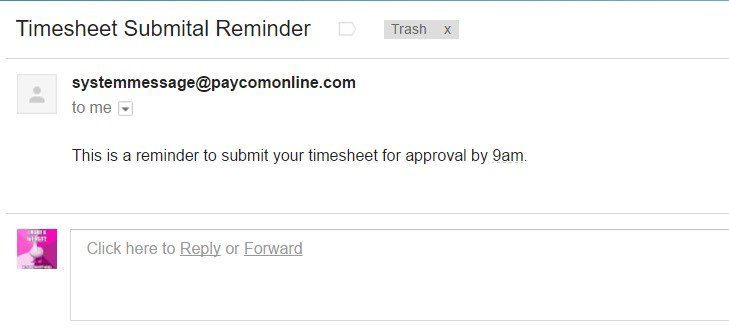 Recently, DocuSign was hacked. They notified users that email addresses were stolen. When this happens, often phishing emails are sent to the list of breached accounts.
The above email was sent to the email addresses obtained in the DocuSign attack. It looks like a harmless message. There is no “call to action” to lure the user into downloading a program or clicking a link. Looking at paycomonlein.com, it looks like it’s a legitimate payroll services site, so it’s a good assumption that the site has been hacked. Most users receiving this email won’t have a paycomonline.com account and won’t use it to submit timesheets.
Though this email looks benign, there is a reason for an attacker to use it. The main objective is to see whether the email is active and can receive messages. This information is very useful for the attacker. Some users would even reply to this email. Replying to the email tells the hacker that the user doesn’t suspect it’s malicious, and allows the attacker to add the user to his “could fall for a phishing attack” list.
The attacker sometimes puts an “unsubscribe” link in the email to trick a user into accessing his private server. This lets the attacker know that the email went directly to the inbox instead of the recipient’s spam box, and it’s a positive signal that the user didn’t recognize that it’s bogus.
This is what your users (when thinking like antimalware) should ask themselves if they receive an email like the above image:
Recently, DocuSign was hacked. They notified users that email addresses were stolen. When this happens, often phishing emails are sent to the list of breached accounts.
The above email was sent to the email addresses obtained in the DocuSign attack. It looks like a harmless message. There is no “call to action” to lure the user into downloading a program or clicking a link. Looking at paycomonlein.com, it looks like it’s a legitimate payroll services site, so it’s a good assumption that the site has been hacked. Most users receiving this email won’t have a paycomonline.com account and won’t use it to submit timesheets.
Though this email looks benign, there is a reason for an attacker to use it. The main objective is to see whether the email is active and can receive messages. This information is very useful for the attacker. Some users would even reply to this email. Replying to the email tells the hacker that the user doesn’t suspect it’s malicious, and allows the attacker to add the user to his “could fall for a phishing attack” list.
The attacker sometimes puts an “unsubscribe” link in the email to trick a user into accessing his private server. This lets the attacker know that the email went directly to the inbox instead of the recipient’s spam box, and it’s a positive signal that the user didn’t recognize that it’s bogus.
This is what your users (when thinking like antimalware) should ask themselves if they receive an email like the above image:
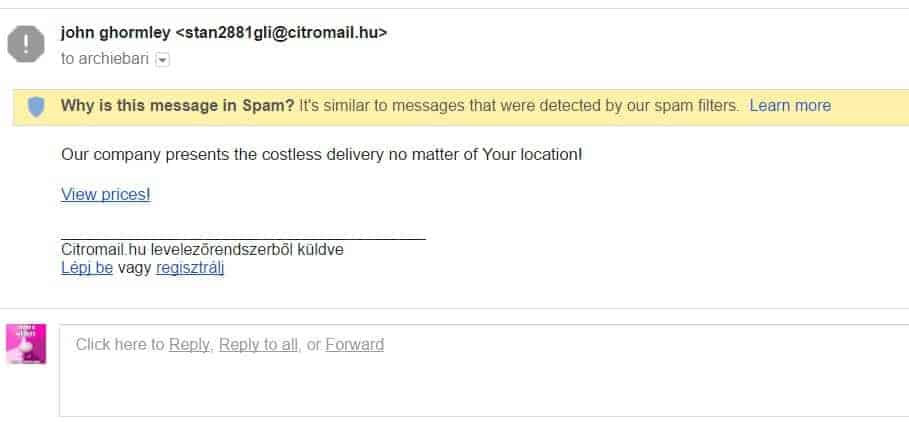
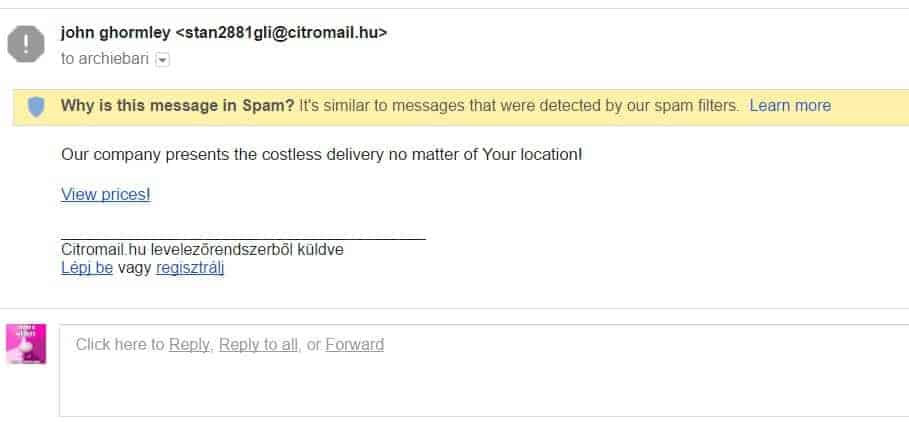 As an IT person, this probably looks incredibly obvious. But Microsoft research has shown that scammers intentionally use obviously bogus messages, for a very clever reason. It allows them to locate the very best targets, those most likely to fall for their scam. You might think no one could possibly fall for this scam, but this sender was probably successful with some recipients.
This message was flagged by the spam filter, of course. But even without the spam notification, there are several red flags that are obvious. Obvious to you, but not to many of your end users. Your challenge is to train your users to think critically, to look for illogical factors, by covering data such as the following.
In this example, the first sign to point out to your users is the language used in the signature. Any professional business matches the signature text with the language of the recipient. If you look at the citromail.hu domain, you’ll see that this is a free email distributor that has no quality checks and balances. Any free email domains including Hotmail, Outlook, Gmail, and Yahoo should automatically send red flags. It doesn’t mean all emails sent from these addresses are malicious, but your users should always take special precautions when receiving emails from these domains.
You can’t see it from this message, but hovering over the link gives you a shortlink. Users should immediately see this as a red flag. Behind the shortlink is a site that distributes malware. The same shortlink is used in the signature. Attackers use shortlinks to avoid malicious link detection from server filters.
This is what your users should ask themselves if they receive an email like the above image:
As an IT person, this probably looks incredibly obvious. But Microsoft research has shown that scammers intentionally use obviously bogus messages, for a very clever reason. It allows them to locate the very best targets, those most likely to fall for their scam. You might think no one could possibly fall for this scam, but this sender was probably successful with some recipients.
This message was flagged by the spam filter, of course. But even without the spam notification, there are several red flags that are obvious. Obvious to you, but not to many of your end users. Your challenge is to train your users to think critically, to look for illogical factors, by covering data such as the following.
In this example, the first sign to point out to your users is the language used in the signature. Any professional business matches the signature text with the language of the recipient. If you look at the citromail.hu domain, you’ll see that this is a free email distributor that has no quality checks and balances. Any free email domains including Hotmail, Outlook, Gmail, and Yahoo should automatically send red flags. It doesn’t mean all emails sent from these addresses are malicious, but your users should always take special precautions when receiving emails from these domains.
You can’t see it from this message, but hovering over the link gives you a shortlink. Users should immediately see this as a red flag. Behind the shortlink is a site that distributes malware. The same shortlink is used in the signature. Attackers use shortlinks to avoid malicious link detection from server filters.
This is what your users should ask themselves if they receive an email like the above image:
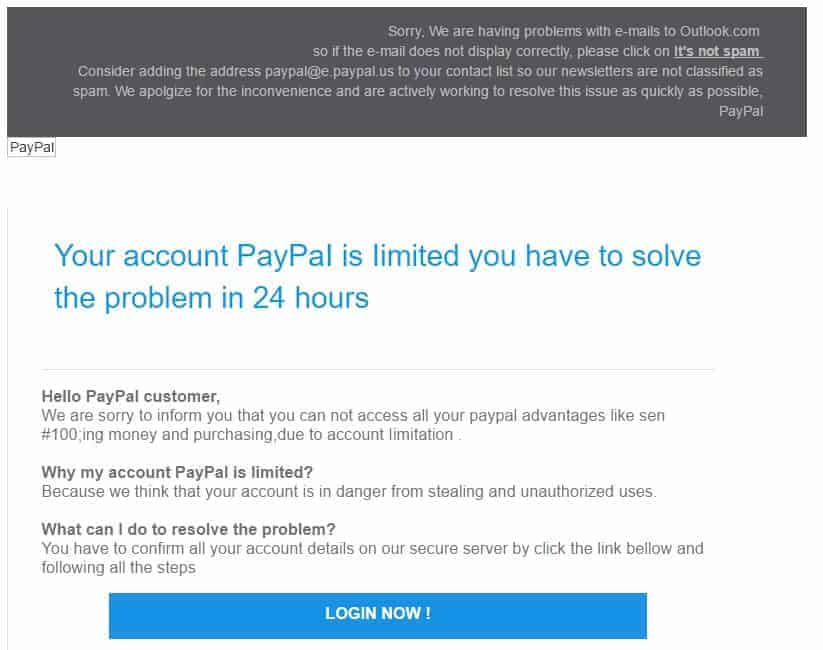 This email was also sent from a free email domain, but there are several new issues with this attempt. First, the attacker tries to get the user to click “Not Spam” in their email client to allow them to stop the filters from sending their messages to spam.
The English is extremely poor, and users should realize that the real PayPal would never send such a poorly worded email. Also, there are some technical errors in the content.
Hovering over the “Login Now” button shows you a different domain than the official PayPal domain. Again, users must be taught the difference between hovering (safe) and clicking (not safe).
This is what your users should ask themselves if they receive an email like the above image:
This email was also sent from a free email domain, but there are several new issues with this attempt. First, the attacker tries to get the user to click “Not Spam” in their email client to allow them to stop the filters from sending their messages to spam.
The English is extremely poor, and users should realize that the real PayPal would never send such a poorly worded email. Also, there are some technical errors in the content.
Hovering over the “Login Now” button shows you a different domain than the official PayPal domain. Again, users must be taught the difference between hovering (safe) and clicking (not safe).
This is what your users should ask themselves if they receive an email like the above image:
 Plenty of consultants try to educate users, but the best way to approach it is to have samples of phishing emails and show users what to look for. Consultants or IT people rarely show users example emails, and this is one reason why security education fails. Just look in your spam folder, and you can find dozens of examples.
If you’re lacking examples, type “online pharmacy” in Google and use a throwaway address to sign up to every site you find. Within days, you will get phishing emails that you can use to educate users.
If you think user education isn’t important, this should change your mind. The security software company Barkly reported on a study which tested how people really behaved when confronted with clever phishing attempts. In the test, 45% of users clicked through on a phishing email but only 20% admitted to it. It’s common for users to keep the fact that they fell for a scam a secret, but you can empower them to understand the signs so that they never engage the attacker.
The Barkly study also reports that there were more phishing attacks in Q1 2016 than in any three-month period since they began tracking it in 2004. IT can only do so much with antimalware and email filtering. You must educate your users to stop the attacks before they become a nightmare on your system. Here are some basic tips to give users more confidence and defend against phishing:
Plenty of consultants try to educate users, but the best way to approach it is to have samples of phishing emails and show users what to look for. Consultants or IT people rarely show users example emails, and this is one reason why security education fails. Just look in your spam folder, and you can find dozens of examples.
If you’re lacking examples, type “online pharmacy” in Google and use a throwaway address to sign up to every site you find. Within days, you will get phishing emails that you can use to educate users.
If you think user education isn’t important, this should change your mind. The security software company Barkly reported on a study which tested how people really behaved when confronted with clever phishing attempts. In the test, 45% of users clicked through on a phishing email but only 20% admitted to it. It’s common for users to keep the fact that they fell for a scam a secret, but you can empower them to understand the signs so that they never engage the attacker.
The Barkly study also reports that there were more phishing attacks in Q1 2016 than in any three-month period since they began tracking it in 2004. IT can only do so much with antimalware and email filtering. You must educate your users to stop the attacks before they become a nightmare on your system. Here are some basic tips to give users more confidence and defend against phishing: